This release of OmniVista Cirrus is available as a free trial or paid version of the full OmniVista Cirrus Solution. The trial version extends for 90 days and can be used to monitor up to 20 Access Point and Switch devices combined (additional time and number of devices can be requested). You can then upgrade from the free trial version to a paid licensed version of OmniVista Cirrus.
OmniVista Cirrus 10.4.2 can be accessed from anywhere, using any approved browser and device (e.g., workstation, tablet). Access to OmniVista Cirrus is supported on the following browsers: Chrome 79+ (on Windows and Redhat/SuSE Linux client PCs), and Firefox 62+ (on Windows and Redhat/SuSE Linux client PCs).
These Production Notes detail features and enhancements, network/device configuration prerequisites, supported devices, and known issues/workarounds in OmniVista Cirrus 10.4.2. Please read the Production Notes in their entirety as they contain important operational information that may impact successful use of the application.
New in This Release
The following sections provide an overview of the features and enhancements introduced with this release.
Devices Supported
Stellar Access Points
The following Wi-Fi Gen6E OmniAccess Stellar Access Points are now supported:
-
OAW-AP1411
-
OAW-AP1431
AOS Switches
The following AOS switch models are now supported:
-
Click here for a list of supported AOS Switch models, which includes supported license information for specific models (Essential and Advanced).
Software Supported
-
AWOS 4.0.8 - OmniVista Cirrus 10.4.2 supports AWOS 4.0.8 on all supported Access Points.
AOS 8.9R1 is the minimum software version supported by OmniVista Cirrus 10. AOS software versions below 8.9R1 are not supported.
-
AOS 8.9R1 – OmniVista Cirrus 10.4.2 now supports AOS 8.9R1 on all supported AOS Switches.
-
AOS 8.9R2 – OmniVista Cirrus 10.4.2 now supports AOS 8.9R2 on all supported AOS Switches.
-
AOS 8.9R3 – OmniVista Cirrus 10.4.2 now supports AOS 8.9R3 on all supported AOS Switches.
-
AOS 8.9R4 – OmniVista Cirrus 10.4.2 now supports AOS 8.9R4 on all supported AOS Switches.
New Features and Functions
This section details new features introduced in this release.
LAN Management
-
Support for provisioning and onboarding AOS switches now available
-
Unified Management with focus on onboarding, inventory catalog, and template-based configuration.
-
Unified Monitoring including new Topology application, new Device details page.
-
Unified Analytics and Assurance (Network Events and Switch Traps)
-
-
OmniVista Cirrus Agent
The OmniVista Cirrus Agent is an independent package that OmniVista Cirrus automatically downloads, installs, and starts on a switch when the switch is added to the Device Catalog. The package consists of a monitoring and configuration agent that interacts on a push-pull, on demand basis with OmniVista Cirrus to manage switches.
-
OmniVista Cirrus 10.4.2 Applications Supporting AP and/or LAN Management
|
Feature |
Stellar AP |
OmniSwitch |
|
Inventory |
||
|
Device Catalog |
|
|
|
Device Troubleshooting |
|
-- |
|
NaaS Device License |
|
|
|
Device Location |
|
|
|
Schedule Upgrades |
|
-- |
|
Access Point Groups |
|
-- |
|
Provisioning Configuration |
|
-- |
|
Wireless |
|
-- |
|
Network Access |
||
|
Unified Access |
|
-- |
|
Authentication Servers |
|
|
|
Groups |
|
|
|
UPAM-NAC |
|
|
|
Accounts |
|
|
|
Network |
||
|
Analytics |
|
|
|
Access Records |
|
|
|
Topology |
|
|
|
Reports |
|
-- |
|
Location |
|
-- |
|
Alerts |
|
-- |
|
Diagnostic Tools |
||
|
Network Events |
|
|
|
Terminal |
|
|
|
Collect Support Info |
|
|
Application Updates/Enhancements
Mesh Configuration Enhancements
-
Configurable Multicast rate control option (default is 24 Mbit/s). The Multicast rate is applied to "Multicast Video Stream" to help reduce jitters in a Mesh environment.
-
Key Management option allows you to select one of the following types of encryption to use for the connections between Mesh/Bridge APs.
-
Both(WPA & WPA2)
-
WPA2-Personal
-
Both(WPA2 & WPA3)
-
WPA3-Personal (Note that when 6G Band is selected, only this key type is available)
-
Note: The11AC model APs do not support key type “Both(WPA2 & WPA3)”, “WPA3-personal” and will reject configuring these encryption key types.
UPAM
UPAM authentication for clients connected to wired ports on AOS Switches.
Network Monitoring and Analytics Enhancements
-
Network Analytics Summary - A network summary at the top of Network Analytics dashboards now displays the following statistics for switches:
-
Number of wired UNP clients.
-
Number of Switches up/down.
-
-
Client Analytics - Improved performance for the Connected Clients Over Time chart.
Stellar AP Syslog Over TLS
An option to enable the use of the TLS encryption method for logging of AP events to a remote Syslog server is now available. When this option is enabled, a Syslog Over TLS Certificate is selected to upload to the AP. Configuring up to four remote Syslog Servers is supported.
Framework Updates
-
Upgrade to Metonic 8 framework for UI/UX.
-
Upgrade MongoDB to 6.0.
-
Quarkus 3.x (Hibernate ORM 5 to 6)
Regulatory Compliance
OmniVista Cirrus 10.4 compliance in US, EU, and abroad:
-
General Data Protection Regulation (GDPR)
-
California Consumer Privacy Act (CCPA)
Third-Party and Open-Source Contributions
-
Free and Open-Source Software (FOSS) Used in OmniVista Cirrus - A list of copyright and license or notices of individual license information is provided for all Open Source Application level components and libraries that OmniVista Cirrus 10 depends upon. To access the list, click on the Free Open Source Software link located at the bottom of every UI screen.
-
A JSON report documenting the usage of third-party FOSS used for OmniVista Cirrus 10 deployment is available.
Network and Device Prerequisites
To ensure the necessary communication between devices (Access Point/Switch) and OmniVista Cirrus 10.4.2, verify/configure the following prerequisites on your local network:
-
Network Prerequisites - Network deployment, bandwidth, proxy, firewall, and NTP server requirements.
-
Device Prerequisites - Supported Access Point software and models.
-
If your fully managed Access Points are running AWOS 4.0.7, please upgrade to AWOS 4.0.8 by setting the Desired Software Version first before accessing OmniVista Cirrus 10.4.2.
-
-
Onboarding Devices Workflow - The basic steps involved to onboard Switches and Access Points for management in OmniVista Cirrus.
-
OmniVista Legacy for Analytics Only Mode - Configure an OmniVista 2500 NMS or OmniVista Cirrus 4 to support communication between Analytics Only Access Point devices and OmniVista Cirrus 10.4.2.
Supported Devices
Stellar Access Points
-
Click here for a list of supported Access Point models:
-
The following Access Point models are not supported:
-
OAW-AP1101
-
OAW-AP1201L
-
OAW-AP1201H
-
OAW-AP1201HL
-
OAW-AP1201BG
-
OAW-AP1261
-
AOS Switches
Click here for a list of supported AOS Switch models.
REST API Management
You can use REST APIs for scripting or integration with any third-party systems in your management network. The complete API reference can be found at the following link based on your region (no login is required):
EU: https://eu.manage.ovcirrus.com/apidoc/apidoc.html
Americas: https://us.manage.ovcirrus.com/apidoc/apidoc.html
For more information, see Automation with APIs.
Known Issues/Workarounds
Inventory
Schedule Upgrade Using Set Desired Software Version (OVNG-10325)
Summary: When an AP already follows a group schedule and the software version is changed using the “Set Desired Software Version” option from the Edit Device drop-down menu, note the following:
-
If the AP Group of the AP device is not part of a schedule upgrade, then the Desired Software Version is set to “Do Not Upgrade”.
-
If the AP Group of the AP device is part of a schedule upgrade, the AP device will be upgraded to the Desired Software Version based on the schedule upgrade for the group.
Workaround: Use the “Information” or “Schedule Software Upgrade” options from the Edit Device drop-down menu to have an AP already following a group schedule upgraded to the specified software version on the next call home.
Cannot Enter Another Username/Password in Terminal Session Modal (OVNG-14678)
Summary: If you enter an incorrect Username/Password when establishing an SSH Terminal Session with a device, an error message is displayed and the Device Credentials modal re-opens. Entering another Username/Password in the modal does not correct the problem, so the SSH connection still fails.
Workaround: Close the Device Credentials modal and the Terminal Session window, then select the device and start a new session.
Auto-Group VLANs Fails to Apply a New Profile to an AP (OVNG-15351)
Summary: The Management VLAN-Based Automatic Grouping option does not work as expected. When you add an AP deice and select the “Mgmt VLAN Based Automatic Grouping” option for the Access Group, the Provisioning Configuration and all existing configurations linked to the matching group are successfully pushed to the AP. However, if any changes are made to the configuration after the AP has onboarded are not pushed to the AP.
Workaround: Edit the AP configuration to manually set an AP Group for the AP.
Cannot Onboard a Virtual Chassis if Adding Two Slave Devices into Device Catalog (OVNG-15331)
Summary: When onboarding a Virtual Chassis (VC) with two Slave switches, provisioning fails if the switches do not use the default Admin account for login credentials. This occurs if the default password for the Admin account was already changed before the VC was onboarded.
Workaround: Set the Initial Configuration again (either the Management User Template or Provisioning Template/Value Mapping). Note that after provisioning fails, only one record shows in the Device Catalog. Search for the device by Serial Number and update the Initial Configuration.
Set Desired Software Version May Fail for Switch VC if Primary Switch Serial Number Doesn’t Match VC Serial Number (OVNG-13619)
Summary: When adding a switch Virtual Chassis (VC) to OmniVista Cirrus, you can enter any Master or Slave serial number that belongs to the VC into the Device Catalog. After the switch sends a Call Home request to OmniVista Cirrus, the record in the Device Catalog is updated to the VC Serial Number (vcSerialNumber). Usually, the serial number of the current Master equals the vcSerialNumber. However, if a VC split, takeover, etc., occurs, the serial number of the current master may not match the vcSerialNumber. This discrepancy may cause problems when attempting to set the Desired Software Version for the VC.
As soon as the VC Switch is added to OmniVista Cirrus (before the device sends a Call Home request) or after the VC Switch becomes managed, you can set the Desired Software Version.
-
If the VC Switch has been added to OmniVista Cirrus but not yet managed, the Desired Software Version changes to 'Do not upgrade' when you add the Master/Slave serial number (not vcSerialNumber).
-
If the VC Switch is managed on OmniVista Cirrus, the Desired Software Version may not display correctly when the Virtual Chassis switches are split or broken.
Workaround: Check the Call Home request sent from the switch Virtual Chassis (VC) in the “/flash/libcurl_log” file. You can access this file by running Collect Support Info on the Switch and downloading it to your computer to examine the contents. Here’s an example Call Home request found in the “/flash/libcurl.log” file showing the VC serial number:
Request data: {"data": {"devices": [{"serialNumber": "V3981563", "deviceMacAddress": "2c:fa:a2:a2:ea:71", "modelName": "OS6560-P24Z8", "partNumber": "903953-90", "role": "master", "hash": "5e9275478352a44861dedbb659523f46b1046eb80eb78e43ecc30c141395e221", "vcSerialNumber": "TMA203981575", "vcMacAddress": "2c:fa:a2:a2:fb:01", "currentSoftwareVersion": "8.9.92.R04", "currentCertifiedSoftwareVersion": "8.9.92.R04", "currentRunningDirectory": "working", "deviceCloudGroup": "-", "authMethod": "certificate", "thinClient": 0, "typeCallHome": "periodic", "deviceMode": "CAPEX", "naasLicenses": []}, {"serialNumber": "TMA203981575", "deviceMacAddress": "2c:fa:a2:a2:fb:01", "modelName": "OS6560-P24Z8", "partNumber": "903953-90", "role": "slave", "deviceMode": "CAPEX"}]}}
When the issue occurs:
-
If the VC Switch has been added to OmniVista Cirrus but not yet managed, manually reset the Desired Software Version for the VC Switch.
-
If the VC Switch is managed on OmniVista Cirrus and is split or broken, complete the following steps:
-
Remove all Chassis entries belonging to the Virtual Chassis switches.
-
Completely reset the Virtual Chassis switches.
-
Add the switch again using the VC serial number from the request (recommendation).
-
ISSU
Cloud Agent Status “Unknown” After ISSU Upgrade on AOS 8.9Rx Switch (OVNG-14310)
Summary: After an ISSU upgrade on an OmniVista Cirrus 10 managed switch, the Cloud Agent Status on the switch is “Unknown”.
Workaround: Manually copy the cloudagent.cfg file from "/flash/working/cloudagent.cfg" to "/flash/issu/cloudagent.cfg" on every managed switch after the ISSU upgrade. This will be fixed in the next AOS 8 release.
License Management
Rogue AP Cleared Alert Is Not Generated if Organization Status Is Update Requested (OVNG-14906)
Summary: If an Organization is waiting for a requested subscription update, “Rogue AP Cleared” alerts are not generated for APs within that Organization.
Workaround: When the Organization update request is approved, “Rogue AP Cleared” alerts are generated.
Need to Wait One Day After License Renewal to Add Devices (OVNG-14988)
Summary: If all licenses are used up, you cannot add new devices to the Device Catalog until new licenses take effect.
Workaround: Wait one day after license renewal to add devices to the Device Catalog.
Network Monitoring
Collect Support Info Feature Does Not Work on NaaS APs that have an expired Management License (OVNG-5850)
Summary: If the NaaS management license expires for an AP in NaaS mode, the Collect Support Info operation will fail.
Workaround: Make sure the NaaS Management License is active when the AP is functioning in the NaaS mode.
Error Message When Filtering Auth Resource Column in Authentication Records List (OVNG-15414)
Summary: When you enter a search value to filter the “Auth Resource” column in the Authentication Records List, an error message is displayed instead of search results.
Workaround: There is no workaround at this time. A fix will be provided in the next release.
Incorrect Event Responder Information When Device is Moved to a Different Site (OVNG-15663)
Summary: When the location of a device is changed to a different Site, the Event Responder page still shows the old site for the device-specific Event Responder.
Workaround: Edit the Event Responder page for the specific device to update the site information.
Final Access Role Profile in Authentication Record Not Updated After Captive Portal Authentication on Switch (OVNG-14892)
Summary: The "Final Access Role Profile" field displayed in the Authentication Record is the Access Role Profile (ARP) that the Switch actually applies to the device after successful Captive Portal authentication, but it is not the ARP that you would expect to apply to the device.
Workaround: There is no workaround at this time.
Start/End Date Values Not Shown When Editing a Report with a Custom Date Range (OVNG-14672)
Summary: When you edit a report that was generated with a custom date range, there is no value displayed for the start and end dates.
Workaround: Enter the dates for the “Start Date” and “End Date” fields when you edit the report.
LLDP Link Information On Device Detail Page Incorrect Between Managed and Unmanaged Switches (OVNG-14208)
Summary: When you click on the “LLDP” tab on the Device Detail screen for a switch, the LLDP link port information may not be correct and some fields blank. This occurs only with an unmanaged switch and a managed switch.
Workaround: There is no workaround at this time.
Link on the Topology Map Is Lost When the Switch Goes Down (OVNG-14922)
Summary: When the switch that an Access Point or another switch is connected to goes down, the link between the two devices disappears from the Topology Map instead of turning red. The Access Point will be linked to Cloud node.
Workaround: There is no workaround at this time.
CSV Analytics Report File Displays More Fields Than the Created Report (OVNG-15429)
Summary: When generating a report in CSV file format, you can select the fields to include in the report. However, the resulting generated CSV report does not include all of the selected fields.
Workaround: There is no workaround at this time.
Completed Wired Client Sessions Not Shown After Device is Deleted (OVNG-15250)
Summary: After deleting a device, wired clients connected to that device are removed from the “Live Wired Clients” list but are still shown as a complete sessions in the “Wired Client Sessions” list. However, you are unable to view additional information for these sessions.
Workaround: There is no workaround at this time.
Save Disabled When Editing the Responder Status (OVNG-15530)
Summary: When you edit a Responder Profile to Enable/Disable the Responder, the Save button is disabled.
Workaround: Delete and recreate the Responder Profile.
Unified Access
Limitation When Selecting an Existing Group for a Unified Policy Condition (OVNG-10669)
Summary: When using the “Choose Existing Group” option for an L2 MAC or L3 IP Policy Condition, if you modify the Group after the Policy is saved and applied to APs, your changes to the Group will not be applied to the APs. This limitation does not occur when using the “Create a New Group” option.
Workaround: After you modify the Group on the Group screen, go to the Unified Policy and select the “Not defined” option (or make any other change to the Policy) and save it. Then edit the Unified Policy again and select the “Choose Existing Group” option.
Creating/Editing Unified Policy With Allowed Special Character Does Not Always Work (OVNG-15415)
Summary: When an allowed special character is used in a Unified Policy name (for example, “&”) you may not be able to create or edit the Unified Policy.
Workaround: Remove the allowed special character.
All of the Special Characters Not Allowed in Unified Policy List Name are Not Specified (OVNG-15404)
Summary: When creating a Unified Policy List with special characters that are not allowed, the “Name” field value prompt does not include all of the special characters that are not allowed. For example, if you enter “PolicyList1&TP1” as the list name, the error message below the “Name” field does not include the “&”.
Workaround: Do not use any special characters in the Unified Policy List Name.
Cannot Edit a Tunnel Profile with “%” or “+” in the Profile Name (OVNG-15410)
Summary: If a Tunnel Profile is created with the “%” or “+” character in the name, you will get an error message when you attempt to edit that profile. This is also true when attempting to edit a Location Policy, Period Policy, RADIUS Server, LDAP Server, MAC Group, Service Group, and Service Policy if the name contains the “%” or “+” character.
Workaround: Do not use these characters in a profile name.
Redirect URL Not Working After Successful BYOD Portal Authentication (OVNG-10674)
Summary: After BYOD Portal Authentication passes, the Success Portal Page displays but the user is not redirected to the “Go to initial URL” specified in the BYOD Access Strategy. This issue occurs only when the initial URL begins with “HTTPS”.
Workaround: No workaround at this time.
UPAM
Errors Occur When the Client Continuously Connects and Reconnects to SSID Portal (OVNG-9735)
Summary: When a user logs into the network, then logs out, and then logs in again, the user may see error messages on the login portal and won’t be able to access the network.
Workaround: User should try to avoid continuously logging in and logging out of the network.
After Upgrading to Android 11 or 12, EAP-TLS Protected Wi-Fi No Longer Works (OVNG-9786)
Summary: In 2021, Android (Google) made a change in their OS to enforce "Validate Server Certificate" option for a 802.1X authentication. This means that, Android 11 and 12 will validate the server's device certificate. Hence users need to specify server's device certificate chain (Root And/Or Intermediate CA's) on their Android devices. If not the authentication will fail. Android 10 and below still works.
Workaround: An alternative is to upgrade the devices to Android 13. Android 13 offers "Trust on First Use" (TOFU) feature. TOFU enables installing the Root CA certificate received from the server during initial connection to a new network. The user must approve installing the Root CA certificate.
Client Unable to Join 802.1X SSID When All EAP = NO and Allowed Method = EAP-TLS for the Access Policy (OVNG-10155)
Summary: When you create an SSID and select an Access Policy with All EAP set to “No” and Allowed Method set to “EAP-TLS” for the SSID Authentication Strategy, the client is unable to join an 802.1X SSID.
Workaround: There is no workaround at this time.
Delay in Seeing BYOD IPv4 Client in the List of BYOD Device Records (OVNG-10759)
Summary: Once a client connects to a BYOD SSID, there is a delay before seeing the Client IPv4 address in BYOD device records. The AP to which the Client is connected will send the client IPv4 with the second accounting packet.
Workaround: No workaround at this time. Problem will be fixed in the next release.
Service Temporarily Unavailable Message With External RadSec Server (OVNG-11277)
Summary: When attempting to authenticate with an External RADIUS Server that is using RadSec ((RADIUS-over-TLS), you may receive a “Service Temporarily Unavailable” message from OmniVista Cirrus.
Workaround: Configure a new External RadSec Server to replace the old one.
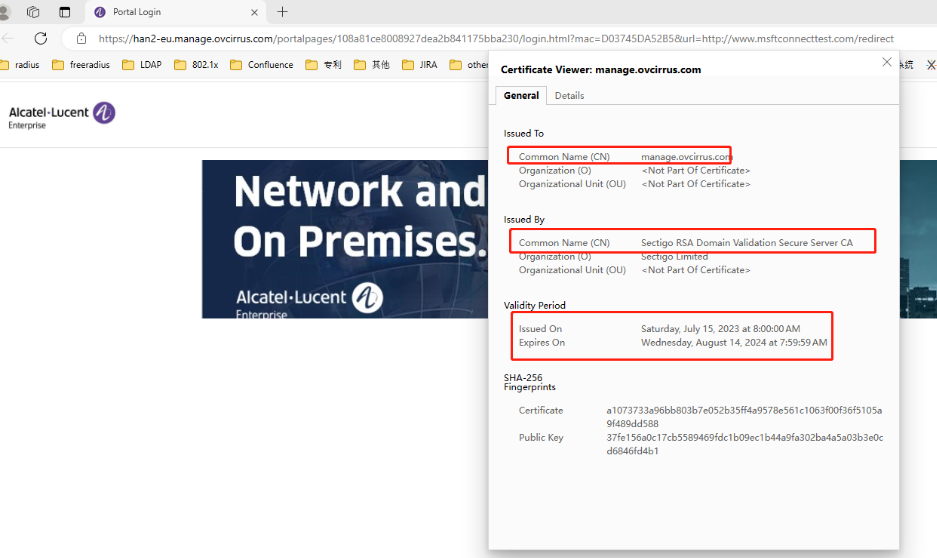
Captive Portal Screen Displayed on Microsoft Edge (OVNG-13528)
Summary: When a guest device using a Microsoft Edge browser opens the Captive Portal Template after connecting to an SSID, the sign in/sign up form may not display (no username, password input shown). If this happens, there may be a mismatch between the hostname the Web browser is attempting to reach and the hostname sent by the Web server in a digital certificate.
Workaround: Click the Lock → Connection is Secure → Certificate Icon on the browser to check if the certificate is correct. For example:
Wireless
Each AP Group Can Only Support Up to Seven SSIDs (OVNG-9610)
Summary: When you try to assign a new SSID into an existing AP Group that already has seven SSIDs, that AP group will not be included into the new SSID.
Workaround: Enable the Extended SSID Scale attribute for the AP Group. When enabled, only AP models that support up to 14 SSIDs can join the AP Group. When disabled, any AP model can join the group, but the limit is 7 SSIDs per AP Group. Note that 6GHz networks do not support the Extended SSID Scale attribute and support only 4 SSIDs per AP Group.
If the SSID Name in a “aproqueinfo.report” Contains a Semicolon, WIPs Alerts and Analytics are Not Generated (OVNG-14205)
Summary: If an AP sends a “aproqueinfo.report” containing an SSID name with a semicolon (“;”), then WIPs Alerts and WIPs Analytics are not generated.
Workaround: Do not use a semicolon character in the SSID name.
Data VPN Setting With Shorthand Mask IP Address Ending in Zero Fails (OVNG-15394)
Summary: If you create a Data VPN Setting profile and specify a Network IP Address for the Shorthand Mask option that ends in zero (10.2.2.0), editing VPN Setting profiles will fail.
Workaround: Avoid specifying a Network IP Address for the Shorthand Mask option that ends in zero. As an alternative, you can use an IP address that ends in .1 (10.2.2.1) to specify a similar IP range.
Other
AP does not Send “portal.report” Event when Wrong Username/Password Entered (OVNG-2811)
Summary: When a user logs in to UPAM Captive Portal with an incorrect username/password, the login will fail but the failure is not immediately indicated on the QoE Analytics UI. Only after 15 minutes will QoE report the failure and the failure is reported as a “Timeout”. Two consequences of this are: Users won’t find out about the failures to login to UPAM Captive Portal until after 15 minutes, and the user will not be able to differentiate between a true “Timeout” with UPAM Captive Portal versus wrong credentials entered at UPAM Captive Portal login.
Workaround: No workaround at this time.
"HostName" Information Lost in “user.report” After the Client Roams to Another AP (OVNG-7792)
Summary: The Client Name (aka “HostName”) information in WLAN Client List is lost after the client roams to another AP.
Workaround: No workaround at this time.
AP Client is Assigned to Untagged VLAN Instead of Tunnel ID Configured in Access Role Profile (OVNG-11683)
Summary: When an Access Role Profile (ARP) with Tunnel only mapping is applied to an AP client, the client is assigned an IP Address in the Untagged VLAN network, not an IP address in the Tunnel network.
Workaround: No workaround at this time.
Issues Fixed
Issues Fixed Since Release 10.4.1
-
Current Client Density Screen Displays Incorrect Session Start Time for AP Clients (OVNG-11243)
-
AP Location is Empty in Live Wireless Client Additional Information (OVNG-12164)
-
Editing the AP Device Location Disrupts Connectivity With the AP (OVNG-12252)
-
Mismatch Between Time Filters on the Client Analytics Screen and the Clients Screen (OVNG-12257)
Issues Fixed Since Release 10.3
-
PKSC8 private key is not supported for LDAP cert and AP Web Cert (OVNG-7726)
-
False Portal Authentication Failure Alert Messages Received (OVNG-11239)
-
Current Client Density Screen Displays Incorrect Session Start Time for AP Clients (OVNG-11243)
Additional Documentation
Online help is available in OmniVista Cirrus and can be accessed by clicking on the Help Link (?) in the upper-right corner of any screen. You can also search through the online help on the OmniVista Cirrus Documentation home page and/or use the following links to familiarize yourself with OmniVista Cirrus 10.4.1 features and functionality:
-
Introducing OmniVista® Cirrus 10
-
Getting Started – What you need to know to get up and running.
-
Configure Organizations for Network Management - How to create and manage Organizations, including creating/modifying sites, adding devices, and adding users.
-
Configure and Manage Device Inventory - Add, edit, or remove Access Point devices from the device inventory. The Device Inventory is also where devices obtain their provisioning configuration when they are added to the inventory.
-
Configure WLAN Network Management- Configure wireless networks, policies to prevent attacks on Stellar AP Series Wireless Devices, and Radio Frequency (RF) profiles for devices. It is also used to configure External Engines and UPAM server certificates.
-
Configure Network Access Control - Configure security functions (authentication, classification) to provide network access controls that are applied to devices attempting to access the network.
-
Monitoring Network Device Activity – Monitor, evaluate, and troubleshoot network components and device activity.
-
Automation with APIs – Develop applications to integrate with OmniVista Cirrus 10.4.1.
-
Troubleshooting - Review general troubleshooting questions and actions for using OmniVista Cirrus. You can also find links to troubleshooting information for specific features.
Technical Support
Alcatel-Lucent Enterprise technical support is committed to resolving our customer’s technical issues in a timely manner. Customers with inquiries should contact us at:
Region Phone Number
North America 1-800-995-2696
Latin America 1-877-919-9526
Europe Union +800 00200100 (Toll Free) or +1(650)385-2193
Asia Pacific +65 6240 8484
Email:ale.welcomecenter@al-enterprise.com
Internet: Customers with Alcatel-Lucent service agreements may open cases 24 hours a day via Alcatel-Lucent’s support web page at: https://myportal.al-enterprise.com/.
Upon opening a case, customers will receive a case number and may review, update, or escalate support cases on-line. Please specify the severity level of the issue per the definitions below. For fastest resolution, please have telnet or dial-in access, hardware configuration—module type and revision by slot, software revision, and configuration file available for each switch.
Severity 1 - Production network is down resulting in critical impact on business—no workaround available.
Severity 2 - Segment or Ring is down or intermittent loss of connectivity across network.
Severity 3 - Network performance is slow or impaired—no loss of connectivity or data.
Severity 4 - Information or assistance on product feature, functionality, configuration, or installation.